Tidal’s Adversary Intelligence team continuously identifies and processes public sources that contain mappings to the MITRE ATT&CK® knowledge base. Our collection mainly involves public threat research & intelligence reports, government advisories, and blogs focused on incident & campaign responses/investigations and malware technical analysis. The Making Waves series takes a data-driven approach to spotlighting ATT&CK techniques that are “trending” in public reporting (or alternatively, techniques that tend to be cited infrequently).
Each edition will enrich the spotlighted techniques with context based on recent threat intelligence. We encourage supplementing this with further context from Tidal’s free Community Edition, which aggregates many relevant supporting resources into a single hub, including defensive & offensive security capabilities from vendors in our Product Registry, detection Analytics, and ATT&CK Groups, Software, Campaigns, & Data Sources. A great place to start pivoting is the Preview or Details page for a technique, such as the one for LSASS Memory (T1003.001) here.
View the summary of Q1 2023’s top TTPs and defensive takeaways with the recording of our recent webinar here.
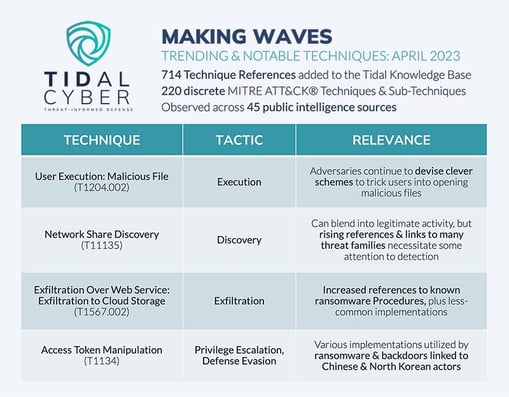 In April, our Adversary Intelligence team added 714 technique references to the Tidal knowledge base, which were observed across 45 public sources. In total, these references covered 220 discrete techniques, or 36% of the 607 techniques & sub-techniques currently included in the ATT&CK knowledge base. Let’s take a closer look at a few trending or otherwise notable techniques from the past month:
In April, our Adversary Intelligence team added 714 technique references to the Tidal knowledge base, which were observed across 45 public sources. In total, these references covered 220 discrete techniques, or 36% of the 607 techniques & sub-techniques currently included in the ATT&CK knowledge base. Let’s take a closer look at a few trending or otherwise notable techniques from the past month:
User Execution: Malicious File (T1204.002)
This technique likely represents some of readers’ earliest exposures to cybersecurity – most of us have known, since an early age, not to open files that appear “sketchy” or otherwise originate from untrustworthy sources! Despite this, we continue to see user execution of malicious files as a common infection trigger, and references to this technique in public reporting have been especially common in recent months (we added 11 in March and 14 in April, a dramatic rise from the low- to mid-single digits most months).
Adversary technique evolution represents a major driver behind the continued success of this seemingly simple technique – actors continually exhibit their ability to craft convincing lures or use clever social engineering tricks to fool users into opening malicious files delivered via phishing emails, compromised websites, and other sources. A fantastic example of this from last month was the reported use of a “leader dot” in the name of a file, likely delivered via targeted social media spearphishing, to conceal a malicious executable as a seemingly benign PDF labeled as a job offer. Last month, user execution of malicious files was also observed during infections involving ransomware, keylogging malware and infostealers, and initial access threats like QakBot.
While layered defenses (including technical safeguards) are always recommended, user awareness of the latest trends in initial infection vectors – and social engineering schemes specifically – is especially important for defense around User Execution. Learn more about current trends in adversary TTP evolution and strategies for mitigating its risks by joining our free webinar on the topic later this month.
Network Share Discovery (T1135)
Discovery techniques have been especially prevalent in Tidal’s dataset in recent times. In past editions of Making Waves and recent webcasts, we’ve discussed how ransomware, infostealers, and more typically perform system checks and search for valuable files and information stored on victim systems before performing their critical exfiltration and/or encryption operations. In April, one of the techniques that saw the overall largest jumps in monthly references was another Discovery technique, Network Share Discovery, which accounted for 11 references, up from low single digit counts in most months.
In April, T1135 references related entirely to ransomware, although reporting covered a range of specific families, including established ones like ALPHV/BlackCat, RagnarLocker, and Clop but also newer ones like Royal and emerging strains Cylance and Money Message. Adversaries can implement the Network Share Discovery technique with short, simple commands to enumerate all file sharing points accessible over the SMB protocol (including via the built-in Windows Net utility). While legitimate use of these commands may be more common in certain environments, leading to event noise, the concentration of threats recently utilizing them should drive up their priority for detection engineering efforts, and several open-source Sigma analytics can be found on the technique’s details page in Tidal Community Edition.
Exfiltration Over Web Service: Exfiltration to Cloud Storage (T1567.002)
While we have periodically observed public reporting callouts to this technique in past months, the seven instances we saw last month represent an especially high tally. T1567.002 refers to adversary exfiltration of victim data to established cloud storage services, rather than over the actors’ primary command & control channels. As the MITRE ATT&CK description for this sub-technique indicates, this exfiltration method “can provide a significant amount of cover to the adversary if hosts within the network are already communicating with the service”.
In recent months, many T1567.002 references in public reports related to ransomware’s use of the Rclone command line program to exfiltrate victim data (to be clear, this isn’t a new phenomenon, but we observed above-average references to the ATT&CK technique identifiers in public reporting in April). Multiple public Sigma rules related to Exfiltration to Cloud Storage using Rclone specifically are clearly apparent on the technique’s details page in Tidal Community Edition, giving defenders a quick starting point for new or tuned behavioral detections. An outlier T1567.002 implementation observed last month came from the CYFIRMA research team’s investigation into FusionCore, an emerging European cybercriminal group, which used multiple tools to exfiltrate victim data over the Telegram API.
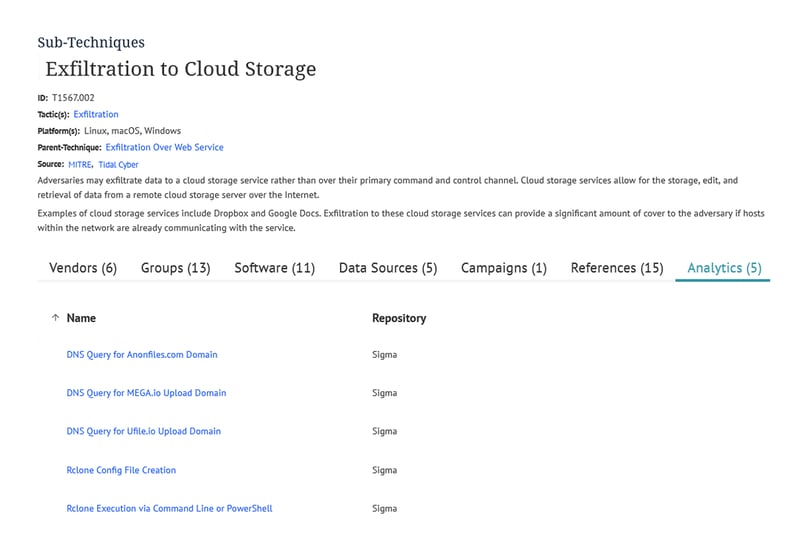
The Exfiltration to Cloud Storage Technique Details page in Tidal’s free Community Edition shows five public Sigma analytics that map to the technique, including some that may be relevant to the technique’s recent implementations observed in the wild (Rclone).
Access Token Manipulation (T1134)
This technique refers to adversary efforts to modify or impersonate tokens that validate user access in a given environment. Several child Sub-Techniques exist under T1134. In recent months, we most often observed the Create Process with Token and Token Impersonation/Theft Sub-Techniques in CTI reporting. Most recent T1134 implementations we observed appeared to be used in order to escalate adversary privileges.
Recent Access Token Manipulation references were again most frequently – although not exclusively – tied to ransomware activity. Other instances related to PortDoor, a Chinese government-linked backdoor malware, and to SimplexTea, a Linux backdoor believed to be associated with North Korea’s Lazarus Group. A total of 37 other malware and six adversary groups of various types are linked on the Tidal Community Edition details pages for T1134 and the two Sub-Techniques spotlighted above. Specific implementations involved suspected duplication of WinLogon tokens and theft of Windows File Explorer tokens via Windows API calls, and creation of new processes, one of which involved use of the built-in runas command. The details pages for T1134.001 and T1134.002 each contain multiple open-source Sigma analytics relevant to those two Sub-Techniques.